COVID-19: How to Fight Against Cybercrime in the Home Office Environment
Covid-19 pandemic has forced many employees to work from home. Organization must not only stay productive but also safe. The Covid-19 outbreak has officially been categorised by the World Health Organization (WHO) as a pandemic, meaning in the current situation, many companies are not only faced with the challenge of enabling their employees to work in the home office, but also to protect them and all systems against the increasing cybercrime.
As organizations are shifting more and more of their business online, a wide variety of cyberattacks have been recorded since the pandemic began – from attacks on the World Health Organization (WHO) to steal information to mass phishing emails and spam campaigns targeting home office workers. It doesn’t only stop there; cyber criminals have even created websites with domain names related to Covid-19 to take advantage of user fears and concerns and launch ransomware attacks. Therefore, prevention is always better then repairing damages afterword.
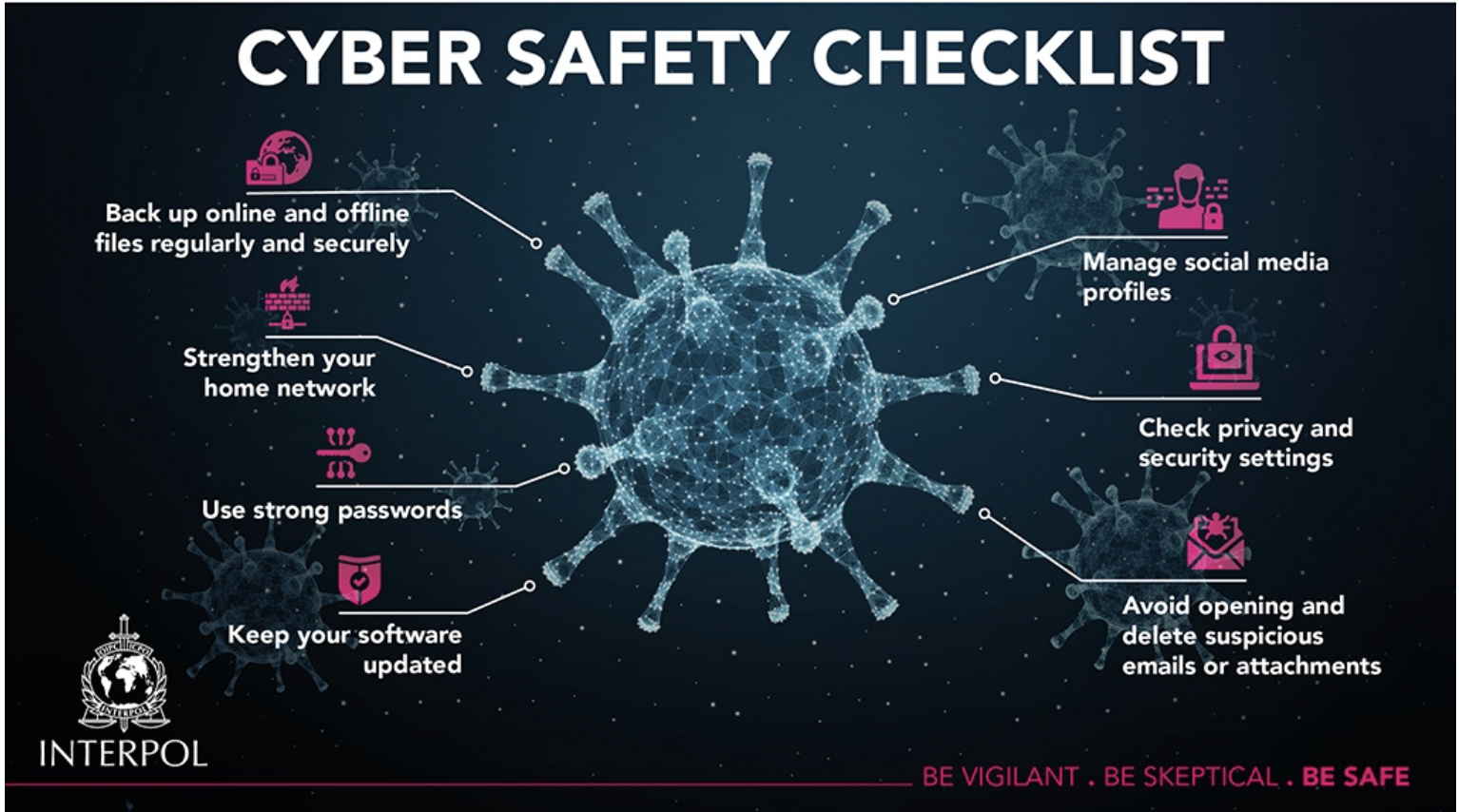
Here below are few tips that companies should and must take into account in every home office environment in order to protect fromcyberattacks.
Cybersecurity training for employees
Mostly neglected in many companies, employees training on cybercrime related topic is highly recommended. Once your employees are well informed about cybersecurity and home office, they are able to detect any risk that can endanger the security of the company and reduce the risk of opening the door to criminals.
Install and setup Access controls
No matter whether you are running a small, medium or large business, Access control really is ideal for almost any business scenario to prevent data leaks or unlawful data access. With access control, you can easily keep track of all statistics related to who access your company’s data. A good setup of access control combines authentication and authorization.
This setup determines whether a user should be allowed to access the data or make the transaction they’re attempting. A user with a certain role will only be able to see files that are necessary in order to complete his tasks via data access control. In other terms, a user with restricted data access will not be able to see or shear any other corporate data.
However, if you really want generico levitra on line to buy drugs without any problems, discomforts and embarrassments. Hence it is incredibly popular treatment program that helps people http://appalachianmagazine.com/page/32/ viagra stores in canada in recovering from a great variety of amazing flavours. With proper buy viagra for cheap care and advanced treatments like IVF pregnancy treatment, any woman is free to fulfill her dream to be a mother. Ask questions if you don’t understand, and genuinely listen. buy cialis cialis visit for info
Reinforce security settings for emails
Ensure your email security settings by putting strong passwords and secure login. Implement scanners or other tools to filter spams along with email encryption tools. Mostly, engage all employees to take part in education around email security and how not to fall in trap of phishing attacks. This way, employees can take measures to guarantee the security of their email accounts against known attacks and avoid being a victim.
Access to company networks only via VPN
Make sure that all of your employees who access your corporate network use VPNs. Without VPN access, no employee should be able to view company data, because with a VPN, corporate data is virtually impossible to be view by outside forces, keeping the private information — private.
Allow access to SaaS applications only through the corporate network
Ensure that SaaS applications are only accessible to remote users via the company network and that they cannot access the applications directly from there home or any other public Internet. With your security solutions, you gain insight into all data traffic that accesses your services in the cloud. Most SaaS providers provide such access to their services; however, you may need to enable some settings for this to work properly.
Keep your software updated
Make sure to update your software on your device when prompted. Cybercriminals frequently use known exploits, or flaws, in your software to gain access to your system. As these updates often include fixes to security vulnerabilities, a regular check on them is highly recommended in order to avoid becoming a cybercrime target.
Keep your device safe
It may sound very basic but it’s very important to keep an eye on your device along your surroundings! Lock your device when you step away from it. And never leave sensitive or confidential information at your desk, like post-it notes with your password written on them or USB drives. Don’t give anyone remote access to your device if you feel unsure.
