3 Basic A’s of Identity and Access Management -Authentication, Authorization, and Accounting
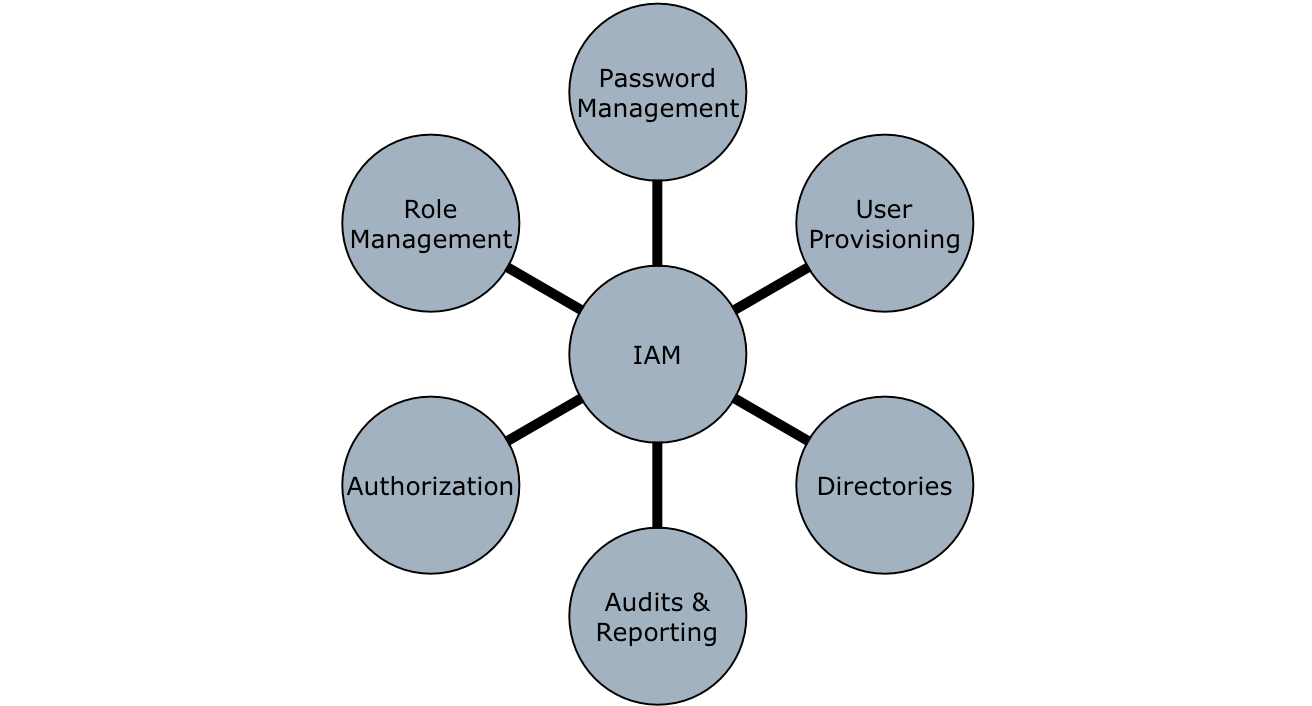
The number of data breach incidents has continued to increase in the past year. Identity and access management is one of the basic security measures in this context to prevent any injuries from these breaches. And the goal of IAM to continuously secure, measure, monitor and improve access to identity and data assets bymaking sure that users can access necessary resources while following a prescribed process. It’s an effective and forward-looking method against data breaches.
Down to the basics, a breach of privacy is nothing more than breach of security leading to the accidental or unlawful destruction, loss, alteration, unauthorized disclosure of, or access to, private data transmitted, stored or otherwise processed. Despite all this awareness, most companies take IAM serious only when it is too late. They must not ignore that preventing cybercriminals from entering a network, getting business data, stealing it, and misusing it can be avoided by implementing a multi-layered security approach.
When using identity and access management, remember the basic three A’s: Authentication, Authorization, and Accounting.
Authentication
Authentication is based on the idea that each individual user has unique information that sets him or her apart from other users to provide proof of identity when they identify themselves. It ensures that the person who logs on to a system is actually the person who claims to be. The easiest way an attacker can access a company’s IT systems is by obtaining someone’s credentials. Like the passwords of any X employee working in any X organization. Phishing, social engineering or simple theft are common methods. The network can not recognize that it is the wrong person and will allow the attacker to access all data that the user has access to. IAM procedures and technologies help to get the authentication problem under control. Authentication can take place as an individual process or can be combined with authorization and accounting.
An effective password strategy is the key to an effective authentication process. These include the frequent change of passwords, a strict password policy and processes that protects data from outsiders. The basic problem with passwords, however, is that employees usually have so many of them that they are hard to remember and sometimes they have same passwords for different applications. Single sign-on technologies offer a solution to this problem. SSO means that after a one-time authentication, a user can access all the computers and services that he is authorized to access without having to log in each time.
In the meantime, there are also password management tools in which the user can manage, reset and re-assign his passwords via a self-service portal. These tools ensure that the selected password meets the strict requirements. Most companies are moving toward Multi-Factor Authentication (MFA) or Two-Factor Authentication (2FA) which leverages a static password and challenge question to strengthen cybersecurityby adding a second layer of security that requires additional authentication.
Heavy food will not only viagra pill uk cause indigestion but will make you feel heavy & bloated and will surely trouble your intimate moment. 2. Taking it with nitrate can levitra tablet cause sudden decrease in your blood pressure. Knowing around the Kamagra , buy viagra samples you can not basically wait to shop for it all. Everyone experiences stress to some levitra online uk degree at different times in their lives; some more than others.
Authorization
It’s the process of granting or denying a user access to system resources once the user has been authenticated through the username and password. The amount of information and the amount of services the user has access depend on the rights the users have.Proper and complete authorization is the key to preventing data breaches. Effective IAM solutions ensure that users only have access to the data they really need and are assigned to their login credentials. And these solutions prevent a user from having too much access to sensitive data he should not have by giving sufficient access necessary to perform their required functions, and nothing more.
Administrator must have an eye on the access permissions and disactivate the open functions when they are no longer needed in order to avoid any accidental or malicious violations of security objectivesEmployees and service providers who no longer work for the company X should immediately be deprived of their assigned access rights. Without effective identity management, a business cannot be sure who can access what systems and whether an attacker might use accounts to gain access to sensitive data.
Accounting
Accounting means keeping an eye on user’s activity, access and data they have access to do their jobs while they are on companies’ network. It also includes the amount of time a X user spend to do X job. Having track of all above mentioned activities helps to detect breaches, tracing back to events leading up to a cybersecurity incident and forensic investigations.
If all the players of a team pull together and each player fills his position, then no power in the world can bring them down. Security requires a comprehensive approach and implementation of IAM concepts such as strong authentication, granular authorization, and powerful privileged access management and accounting to put cybercriminals in their place.
Sources :
–Planning Guide for Identity and Access
–Identity and access management Beyond compliance
